When you see the message " 'This application is bound to' 62893", it signifies that a program on your computer is operational and ready to process incoming requests on that specific port. Port 62893 isn't a commonly used port for standard applications, so it's likely associated with a unique software you have installed.
It's important to note that this message itself doesn't necessarily indicate any security issues. However, if you are unfamiliar with the program running on port 62893, it is always wise to examine it further to ensure its legitimacy and potential impact on your system.
A Mystery Socket on 127.0.0.1:62893
Encountering an suspicious socket at this specific port, 127.0.0.1:62893, can often indicate a range of potential causes. Firstly this specific identifier could be associated with running software on your system. However, it's important to investigate further its origin and purpose to rule out any potential harms.
- Utilizing system tools can help identify the application utilizing this socket.
- Researching online resources dedicated to system diagnostics might provide useful information
- Regularly maintain your software to mitigate potential threats
Analyzing Connection to 127.0.0.1:62893
This demonstrates a connection attempt to the local machine running on port 52893. The IP address, 127.0.0.1, refers to the localhost, meaning that the connection is originating from within the {samemachine itself. Additional analysis of this connection may involve examining the protocol used and the program responsible for initiating it.
Potential Backdoor on localhost:62893
A suspected backdoor has been detected on port 62893 of your local machine. This suggests that an attacker may have established unauthorized control to your system. It is crucial to investigate this issue immediately and take necessary steps to secure your network.
- Avoid from accessing any sensitive information or data on your machine.
- Isolate your machine from the internet until the issue is resolved.
- Perform a thorough scan of your system for malicious software.
- Update all applications to the latest releases
If you are uncertain about how to proceed, it is strongly to seek assistance a cybersecurity professional.
Analyzing TCP Stream on 127.0.0.1:62893
A TCP stream originating from the local machine on port 62893 can provide valuable insights into ongoing network activity. This particular port is often used for applications or services that require a reliable and ordered data transmission check here protocol like TCP. By examining the characteristics of this stream, such as its path, payload content, and timestamped events, you can obtain a deeper knowledge of what processes are interacting on your system.
- Interpreting the stream's packet headers can provide information about the protocol version, source and destination addresses, sequence numbers, and other crucial metadata.
- Dissecting the payload content itself can help in identifying the type of data being transmitted, whether it's plain text, binary code, or multimedia files.
- Observing the stream over time can demonstrate patterns and anomalies in network behavior, potentially indicating unusual interactions.
Troubleshooting Process Using 127.0.0.1:62893
When encountering issues with a program or application, developers often employ a debugging process to pinpoint and resolve the underlying cause of the issue. 127.0.0.1:62893 functions as a common endpoint within this workflow.
Connecting 127.0.0.1:62893 permits developers to monitor program execution in real-time, offering valuable insights into the behavior of the code. This can involve examining variable values, inspecting program flow, and spotting particular points where errors occur.
- Leveraging debugging tools that interact with 127.0.0.1:62893 can significantly augment the debugging process. These tools often provide a graphical view of program execution, making it more straightforward to interpret complex code behavior.
- Productive debugging requires a systematic approach, including carefully reviewing error messages, isolating the affected code segments, and testing potential corrections.
 Joseph Mazzello Then & Now!
Joseph Mazzello Then & Now! Michelle Trachtenberg Then & Now!
Michelle Trachtenberg Then & Now!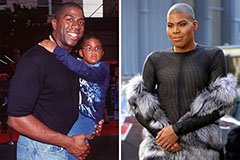 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Susan Dey Then & Now!
Susan Dey Then & Now!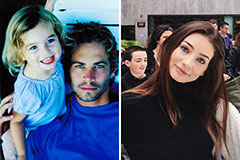 Meadow Walker Then & Now!
Meadow Walker Then & Now!